On 30 March 2022, the Department for Digital, Culture, Media and Sport published its annual Cyber Security Breaches Survey (the “Survey”) – UK’s official cyber resilience study. According to the gov.uk website, the Survey is primarily used to inform the Government’s policy on cyber security.
The Survey was conducted by a random probability telephone interview across 1,243 businesses, 424 charities and 420 education institutions Split into 7 chapters, the Survey contains analysis includes the participants’ general approach to cyber security, handling of cyber incidents, general awareness of threats etc. The Survey also contains a “Key Findings” chapter which provides an executive summary of the conclusions made in the Survey.
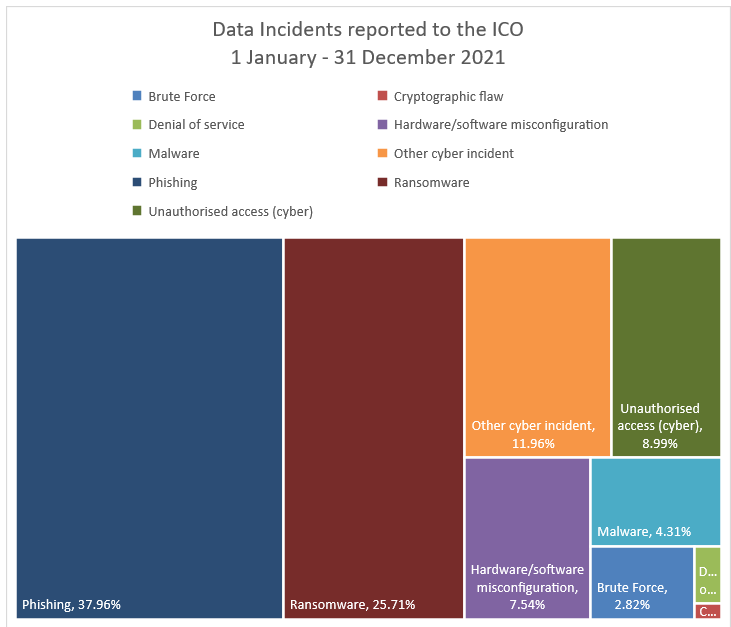
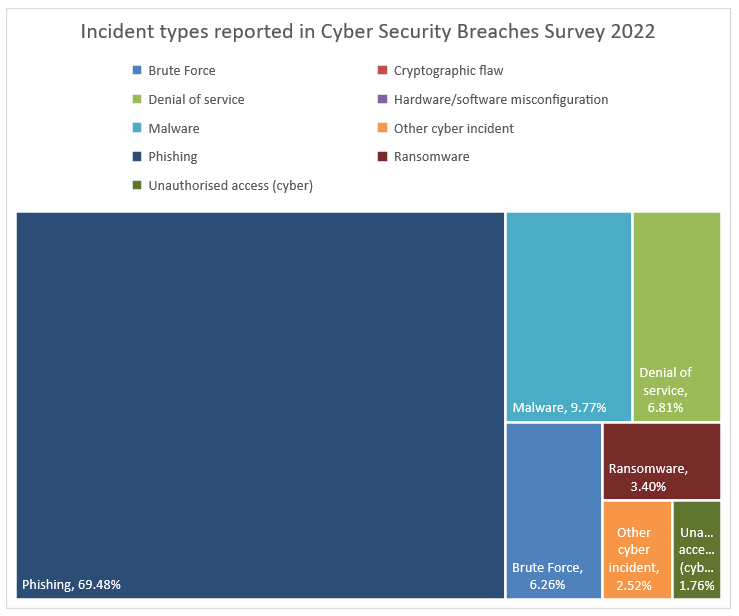
We have compared “incident type” data from the Survey against publicly-available statistics published by the UK Information Commissioner’s Office (“ICO”) for the same time period (1 January to 31 December 2021).
While the number of participants in the Survey is significantly lower than organisations who have reporting obligations towards the ICO under various privacy and network security legislation, the proportion of incident types provides valuable insights on the type of attacks businesses and organisations face on a daily basis. On the other hand, the ICO only receives data breach notifications regarding security incidents which pass the risk severity threshold in Article 33 UK GDPR, meaning that the regulator only handles incidents which have resulted in actual or likely risk to individuals.
What do the statistics show?
According to both the Survey and the ICO statistics, phishing attacks are the most common type of cyber incident – with nearly 70% reported by Survey participants and 38% recorded by the ICO. While an unsuccessful phishing attack does not in itself constitute a data breach, those reported to the ICO have presumably resulted in risk to data subjects due to unauthorised access to an email or other account (also known as “Business Email Compromise” or “BEC”). Consequently, the numbers can lead to a conclusion that over the past year, just under 50% of organisations who have experienced phishing attacks have actually fallen victim to one or more of these, resulting in a data breach. However, when the “Phishing” and “unauthorised access” categories in the ICO data are combined, the proportion of victims jumps to over 50%.
The other curious difference in the data related to ransomware. While a major proportion of cyber incidents reported to the ICO, it only takes up less than 4% of the incidents identified in the Survey data. One might conclude, therefore, that whilst the volume of phishing attacks are high and suffered by many businesses, they do not result in a risk to data subjects and a notification to the ICO.
Why is there a difference in the data?
Due to the ease of implementation, phishing attacks (including SMShing and other social engineering scams) form part of the everyday reality for most UK organisations. However, they are also the most easily avoidable vulnerabilities, provided that organisations invest resources in staff training and technology solutions to minimise the risk of a successful phishing attack. Many business in the country have acknowledged this and provide regular training and simulated phishing campaigns, to maintain staff engagement and readiness. While phishing clearly remains the biggest attack vector in reportable data breaches, the percentage of successful attacks is encouragingly low. The National Cyber Security Centre (NCSC) recommends a 4-layer approach to phishing defences for individual organisations, available here.
With regards to ransomware, these surveys highlight the relative seriousness: a successful attack can be truly destructive and will more often lead to regulatory notifications. In particular, where data is lost due to unavailable backups or exfiltrated and hosted publically on a “shaming” Dark Web site. The NCSC has published a 4-step plan for organisations to ensure maximum preparedness against the threat of ransomware.
These differences also go to highlight the importance of not simply focussing on preventing one attack vector. A balanced approach to avoiding both the attritional and devastating cyber attacks must be taken.
Footnote
The ICO breach notification data is available as quarterly reports at https://ico.org.uk/action-weve-taken/data-security-incident-trends/